没有合适的资源?快使用搜索试试~ 我知道了~
inside_windows_rootkits
需积分: 9 41 下载量 28 浏览量
2009-06-11
14:29:10
上传
评论
收藏 1.04MB PDF 举报
温馨提示

试读
28页
inside_windows_rootkits rootkits绝好的入门资料,娓娓道来Rootkit
资源推荐
资源详情
资源评论

2006 VigilantMinds Inc. All rights reserved
Inside Windows Rootkits
Chris Ries
Security Research Engineer
VigilantMinds Inc.
4736 Penn Avenue
Pittsburgh, PA 15224
info@vigilantminds.com
Inside Windows Rootkits
May 22, 2006
2006 VigilantMinds Inc. All rights reserved
- 1 -
Introduction
Although they have been around for quite some time, rootkits have become somewhat of a
buzzword in the security industry over the past year. While rootkits have traditionally been used
by sophisticated attackers to hide their presence on compromised machines, recent worms,
viruses, and trojans have started using them to complicate efforts to detect and clean infected
machines. Microsoft recently reported that over twenty percent of the malware found by their
malicious code removal tool on Windows XP Service Pack 2 machines contained rootkit
technology [1]. By hiding the infection, rootkits allow the malicious software to remain on the
system for a longer period of time. This enables the malicious software to steal more information,
send out more spam, launch more DDOS attacks, and ultimately make more money for whoever
is controlling it. Even some commercial software has adopted techniques used by rootkits for
protection. The most famous example of this is the Sony Digital Rights Management (DRM)
software that received intense media attention and criticism in late 2005. While the DRM
software may have been hiding itself for protection, many considered this behavior to be
unethical. Malicious software could also use the DRM software’s rootkit capabilities to hide
malicious files on infected machines.
The goals of this paper are to take a detailed look at how rootkits work, what they do, and what
can be done to detect and prevent them. Stealth techniques used by today’s rootkits will be
explained, and detection of rootkits will be illustrated using examples of malicious software found
in the wild.
Like any other area in security, the current state of rootkits is an arms race between the rootkit
authors and those responsible for protecting systems from their harmful effects. Because of this,
proof of concept rootkits are constantly being released to demonstrate new methods of bypassing
current rootkit detection and prevention mechanisms. Eventually, some of these proof of concept
rootkits are transformed into production rootkits that make their way into the hands of attackers
and malware authors on the Internet. This paper examines several current proof of concept
rootkits that may become more common in malware, as well as rootkits that have already been
released into the wild.
Inside Windows Rootkits
May 22, 2006
2006 VigilantMinds Inc. All rights reserved
- 2 -
Rootkits 101
What is a Rootkit?
Before getting too deep into the subject, it is important to understand exactly what rootkits are.
The goal of a rootkit is to provide an attacker or malicious code with a permanent, undetectable
presence on a computer. Typically, this involves hiding the presence of resources such as
processes, files, registry keys, and open ports that are being used by the malicious entity.
Additionally, a rootkit may provide a covert channel between the computer and a remote host that
is controlled by an attacker. A rootkit allows an attacker, worm, or trojan to hide from users,
administrators, as well as security software on both the computer and the network. In some
cases, it can even be used to hide from forensics experts.
History of Rootkits
While many early viruses utilized rootkit-like stealth techniques, rootkits did not appear until the
1990’s when attackers built “kits” to help them set up shop on compromised hosts. Most of these
kits were built for UNIX systems due to the dominance of UNIX on the Internet at the time.
Attackers would use the kit to gain and maintain “root” privileges on the compromised machine.
The kit would provide backdoor access, and may also replace system binaries such as ‘ls’, ‘ps’,
and ‘netstat’ with copies that would hide resources belonging to the attacker. For example, the
attacker may place a modified version of netstat on compromised machines that hides open ports
associated with backdoors. To combat these attacks, administrators began to use tools such as
Tripwire to monitor system binaries for changes. The arms race continued, and rootkits
eventually made their way into the kernel of the UNIX operating systems being targeted by
attackers. Eventually, this cat-and-mouse game made its way over to the world of Windows,
leading to many of the Windows kernel rootkits that are popular today.
How Rootkits Are Used
Network attacks can usually be broken down into the following phases:
1. Attacker discovers a vulnerability on a target system.
2. Attacker exploits the vulnerability to gain access to the system.
3. Attacker gains a stronger foothold on the compromised system by collecting information,
installing backdoors, etc.
4. Attacker utilizes system access to achieve the ultimate goals of the attack. In cases of
malware, the ultimate goals may be to steal information, disseminate spam, or launch a denial of
service attack against other systems.
5. Eventually the compromise may be discovered, and incident response will be executed.
Note that all of these steps do not occur during every attack. For example, an attacker may gain
access to a system, steal a specific piece of information, and then never return to the system
again. If the attacker was smart enough to leave no signs, the compromise may never be
detected, thus eliminating the phase of incident response. Also, if the attacker were an insider,
he or she may already have access to the system, so there would be no need to discover and
exploit a vulnerability. Nonetheless, a subset of these phases occurs in almost every network
attack.
Rootkits are usually introduced into the attack during the third phase, when the attacker attempts
to gain a stronger foothold on the compromised system. A rootkit can facilitate this phase by
providing stealth remote access to the compromised machine. It can also help to hide the
attacker's presence by hiding his or her files, registry keys, network activity, and processes, which
Inside Windows Rootkits
May 22, 2006
2006 VigilantMinds Inc. All rights reserved
- 3 -
can postpone or even eliminate discovery of the compromise. This allows the fourth phase of the
attack to occur for a longer period of time, which is usually the phase that is most beneficial for
the attacker and devastating to the victim.
Oftentimes a system compromise or malware infection is detected by unusual network activity,
strange process behavior, or degraded performance on a system. Rootkits, however, are able to
conceal network activity and hide processes. When investigating performance issues on a
system, users typically rely on Windows tools such as Task Manager and netstat, or third party
tools such as HijackThis or Process Explorer. Most rootkits work at a level much lower than
these tools, which means that the tools will be unable to see the malicious resources on a system
that has been compromised. At the very least, a rootkit will make detection of a compromise and
cleaning of a system more time consuming and difficult. In the worst case, the rootkit may
prevent detection and cleaning altogether.
How Rootkits Work
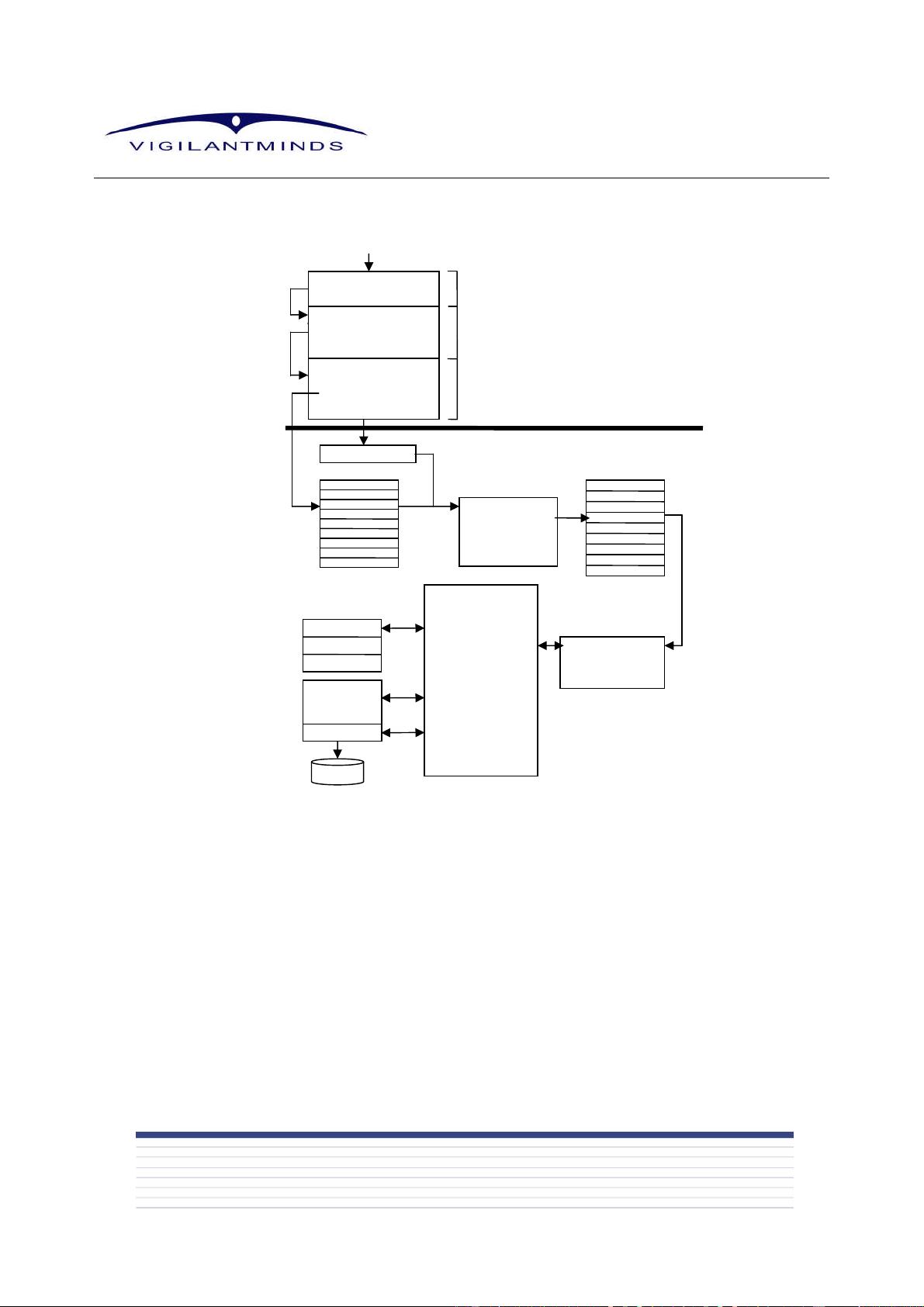
Before digging into the details of the various methods used by rootkits to hide resources, let’s
take a step back and walk through all of the steps involved in accessing a resource. For
example, consider a situation where a user requests a listing of files that are located in a
particular directory. To accomplish this, a user will typically communicate with a command-line
interface of a user process such as cmd.exe, or with a graphical user interface of a user process
such as explorer.exe. After receiving these requests from user input, these processes will
typically use the Win32 API to complete the request. One of the most common methods of listing
files with the Win32 API is to use the FindFirstFile() and FindNextFile() functions exported by
kernel32.dll [2]. FindFirstFile() is first passed the directory name, and if the function succeeds it
returns a handle that can then be passed to FindNextFile() to enumerate the remaining files in the
directory. From an application developer’s perspective using these functions is very simple, but a
lot of steps are completed under the hood of the operating system each time these functions are
called (These steps are illustrated in Figure 1).
After being called by the application’s code, the FindNextFile() function calls the
NtQueryDirectoryFile() Native API function which is located in ntdll.dll. This function takes many
more arguments than FindNextFile(), making its usage much more complex. The complexity of
this function is the reason that Microsoft provides the FindNextFile() function as a simpler
interface for application developers. The ultimate goal of the NtQueryDirectoryFile() function
located in ntdll.dll is to get the kernel-mode NtQueryDirectoryFile() system service to execute
1
.
Like all other Native API functions exported by ntdll.dll, NtQueryDirectoryFile() acts as a user-
mode wrapper for the kernel-mode system service of the same name.
For security reasons, Microsoft Windows does not allow user-mode code to directly call kernel-
mode code. If user-mode code needs to get kernel-mode code to execute, it needs to use a
special mechanism to indirectly call the kernel-mode code. Therefore, in order to accomplish its
goal of executing its corresponding kernel-mode system service, the NtQueryDirectoryFile()
function needs to utilize this mechanism. How the mechanism works depends on the specific
version of Windows being used. Windows XP and later versions of the operating system adopted
a different method than older versions in order to increase performance.
1
For a detailed explanation of kernel-mode vs. user-mode privileges, see Appendix A.
Inside Windows Rootkits
May 22, 2006
2006 VigilantMinds Inc. All rights reserved
- 4 -
Figure 1: The various steps involved in completing a call to the FindNextFile function.
In Windows 2000 and earlier versions of the NT operating system family, software interrupts are
used to call kernel-mode code from user mode. An interrupt is essentially a method of telling the
CPU that a specific event has occurred that needs to be handled. When an interrupt occurs, the
CPU checks the Interrupt Descriptor Table (IDT) to determine what code should handle the event,
and then executes that code. Following the directory listing example, the NtQueryDirectoryFile()
function in ntdll.dll moves a number into the EAX register that specifies which system service it is
trying to call, then it executes an ‘INT 0x2e’ instruction to cause a software interrupt to occur. The
0x2e passed to the interrupt instruction specifies that the interrupt occurred because a system
service was requested. Once the interrupt occurs, the processor uses the number 0x2e as an
offset into the IDT in order to locate the code responsible for handling the interrupt. The 0x2e
entry of the descriptor table specifies the address of the System Service Dispatcher (also known
as KiSystemService), which is the code responsible for handling system service calls. The CPU
loads the address of the System Service Dispatcher from the table into the Instruction Pointer
register, and the dispatcher executes.
CALL FindNextFile
FindNextFile:
…
CALL
NtQueryDirectory File
NtQueryDirectoryFile::
MOV EAX, XX
INT 2E / SYSENTER
IA32_SYSENTE
Interrupt Descriptor Table (IDT)
System Service
Dispatcher
(KiSystemService)
System Service
Dispatch Table
(SSDT)
2E
XX
NtQueryDirectoryFile
I/O Manager
Filesystem Driver Stack
NTFS Driver
AV Filter Driver
Volume
Manager
Disk Driver
Disk Driver
Backup Driver
User-mode
Kernel-mode
User program.exe
Kernel32.dll
Ntdll.dll
User Input
剩余27页未读,继续阅读
资源评论

wangxingxing
- 粉丝: 0
- 资源: 7
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- 软件仿真多机串行通信.doc
- Python大作业:音乐播放软件(爬虫+可视化+数据分析+数据库)
- 课程设计-python爬虫-爬取日报,爬取日报文章后存储到本地,附带源代码+课程设计报告
- 软件和信息技术服务行业投资与前景预测.pptx
- 课程设计-基于SpringBoot + Mybatis+python爬虫NBA球员数据爬取可视化+源代码+文档+sql+效果图
- 软件品质管理系列二项目策划规范.doc
- 基于TensorFlow+PyQt+GUI的酒店评论情感分析,支持分析本地数据文件和网络爬取数据分析+源代码+文档说明+安装教程
- 软件定义无线电中的模拟电路测试技术.pptx
- 软件开发协议(作为技术开发合同附件).doc
- 软件开发和咨询行业技术趋势分析.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功