
Interoperability Specification for ICCs
and Personal Computer Systems
Part 8. Recommendations for ICC Security and
Privacy Devices
Apple Computer, Inc.
Axalto
Gemplus SA
Infineon Technologies AG
Ingenico SA
Microsoft Corporation
Philips Semiconductors
Toshiba Corporation
Revision 2.01.01
September 2005

Copyright © 1996–2005 Apple, Axalto, Gemplus, Hewlett-Packard, IBM, Infineon, Ingenico, Microsoft,
Philips, Siemens, Sun Microsystems, Toshiba and VeriFone.
All rights reserved.
INTELLECTUAL PROPERTY DISCLAIMER
THIS SPECIFICATION IS PROVIDED “AS IS” WITH NO WARRANTIES WHATSOEVER INCLUDING
ANY WARRANTY OF MERCHANTABILITY, FITNESS FOR ANY PARTICULAR PURPOSE, OR ANY
WARRANTY OTHERWISE ARISING OUT OF ANY PROPOSAL, SPECIFICATION, OR SAMPLE.
NO LICENSE, EXPRESS OR IMPLIED, BY ESTOPPEL OR OTHERWISE, TO ANY INTELLECTUAL
PROPERTY RIGHTS IS GRANTED OR INTENDED HEREBY. AXALTO, BULL CP8, GEMPLUS,
HEWLETT-PACKARD, IBM, MICROSOFT, SIEMENS NIXDORF, SUN MICROSYSTEMS, TOSHIBA, AND
VERIFONE DISCLAIM ALL LIABILITY, INCLUDING LIABILITY FOR INFRINGEMENT OF
PROPRIETARY RIGHTS, RELATING TO IMPLEMENTATION OF INFORMATION IN THIS
SPECIFICATION. AXALTO, BULL CP8, GEMPLUS, HEWLETT-PACKARD, IBM, MICROSOFT, SIEMENS
NIXDORF, SUN MICROSYSTEMS, TOSHIBA, AND VERIFONE, DO NOT WARRANT OR REPRESENT
THAT SUCH IMPLEMENTATION(S) WILL NOT INFRINGE SUCH RIGHTS.
Windows and Windows NT are trademarks and Microsoft and Win32 are registered trademarks of Microsoft
Corporation.
PS/2 is a registered trademark of IBM Corp. JAVA is a registered trademark of Sun Microsystems, Inc. All
other product names are trademarks, registered trademarks, or servicemarks of their respective owners.
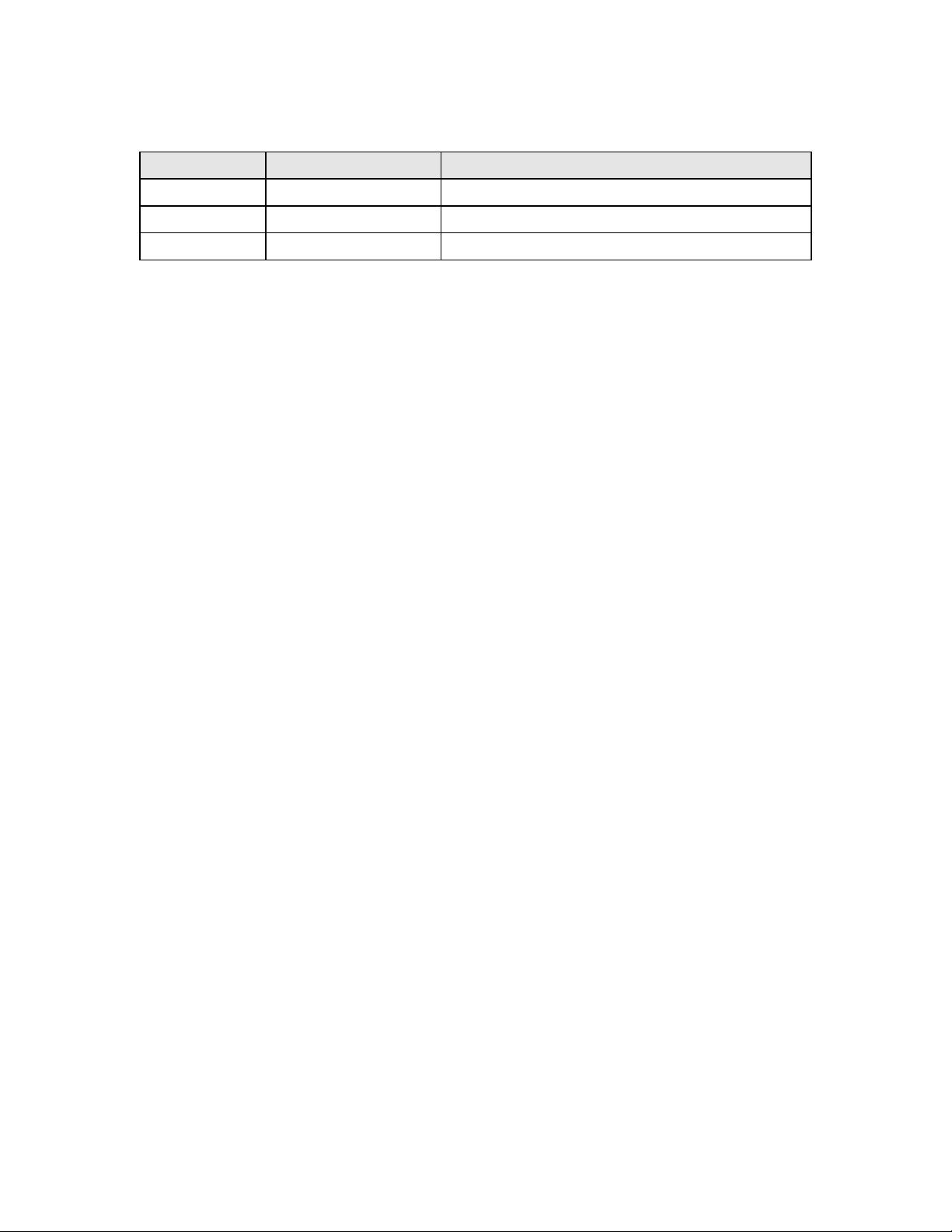
Revision History
Revision Issue Date Comments
2.00.01 May 28, 2004 Spec 2.0 Final Draft
2.01.00 June 23, 2005 Final Release
2.01.01 September 29, 2005 Changed Schlumberger to Axalto
Interoperability Specification for ICCs and Personal Computer Systems
Part 8. Recommendations for ICC Security and Privacy Devices
Contents
1 SCOPE 1
2 CRYPTOGRAPHIC SERVICES 3
2.1 Required Algorithms 3
2.1.1 Hashing 3
2.1.2 Digital Signatures 3
2.1.2.1 RSA 3
2.1.2.2 Digital Signature Algorithm (DSA) 4
2.1.3 Key Exchange 5
2.1.3.1 RSA Key Exchange 5
2.1.3.2 Diffie-Helman Key Exchange 6
2.1.4 Symmetric Ciphers 6
2.2 Random Number Generation 7
2.2.1 Increasing Entropy 7
2.3 Key Generation 7
2.3.1 Determining Prime Numbers 8
2.3.1.1 Generation 8
2.3.1.2 Primality Testing 8
2.3.1.3 RSA Keys 9
2.3.1.4 DSA 10
2.3.1.5 Symmetric Algorithms 10
3 AUTHENTICATION SERVICES 11
3.1 User Authentication to Remote Entities 11
3.1.1 Shared Secret Challenge-Response Protocol 11
3.1.2 Enhanced Shared Secret Challenge-Response Protocol 12
3.2 Public Key-Based Protocol 14
3.3 Authentication to the ICC 15
3.3.1 Cardholder Verification 16
3.3.2 Application Verification 16
3.3.3 Invalid Attempt Limits 17
3.4 ICC Authentication 17
4 STORAGE SERVICES 19
4.1 File Types Supported by the Operating System 19
4.1.1 The Master File (MF) 19
4.1.2 The Dedicated Files (DF) 19
4.1.3 The Elementary Files (EF) 20
1996–2005 PC/SC Workgroup. All rights reserved. Page i

Interoperability Specification for ICCs and Personal Computer Systems
Part 8. Recommendations for ICC Security and Privacy Devices
4.1.3.1
Transparent Files 20
4.1.4 File References 20
4.1.5 File Control Information 21
4.2 Access Control 21
4.2.1 Access-Control Modes 21
4.3 Access Control Enforcement 21
4.4 CHV Authentication State 22
4.5 APP Authentication State 23
5 SPECIAL FILES 24
5.1 Special Elementary Files 24
5.1.1 CHV Code File 24
5.1.2 APP Secret File 24
5.2 Mandatory Files 25
5.2.1 Master File 25
5.2.2 MASTER CHV Code 26
5.3 Cryptographic Files 26
5.3.1 Cryptographic DF 26
5.3.2 Cryptographic Algorithm EF 27
5.3.3 RSA Private Signing Keys 27
5.3.4 RSA Public Signing Keys 28
5.3.5 DSA Private Signing Keys 28
5.3.6 DSA Public Signing Keys 28
5.3.7 RSA Private Key Exchange Keys 29
5.3.8 RSA Public Key Exchange Keys 29
5.3.9 Diffie-Helman Constants 29
5.3.10 User Secrets 29
5.4 ICC Identification Files 30
5.4.1 ICC Identification DF 30
5.4.2 ICC Identification EF 30
5.4.3 ICC Identification Private Key 31
5.4.4 ICC Identification Public Key 31
6 ATR REQUIREMENTS 32
7 RECOMMENDED COMMANDS AND FUNCTIONAL BEHAVIOR 33
7.1 Command Summary 33
7.2 Functional Description 34
7.2.1 Common Status Codes 34
7.2.2 Security Relevant Instructions 35
1996–2005 PC/SC Workgroup. All rights reserved. Page ii















- 1
- 2
前往页