没有合适的资源?快使用搜索试试~ 我知道了~
CompTIA Security+ 学习指南
需积分: 50 21 下载量 21 浏览量
2020-01-24
14:20:11
上传
评论 2
收藏 7.61MB PDF 举报
温馨提示

试读
36页
professor-messer-comptia-sy0-401-security-plus-study-guide-v5
资源推荐
资源详情
资源评论
Professor Messer’s
CompTIA Security+
SY0-401 Study Guide
hp://www.ProfessorMesser.com
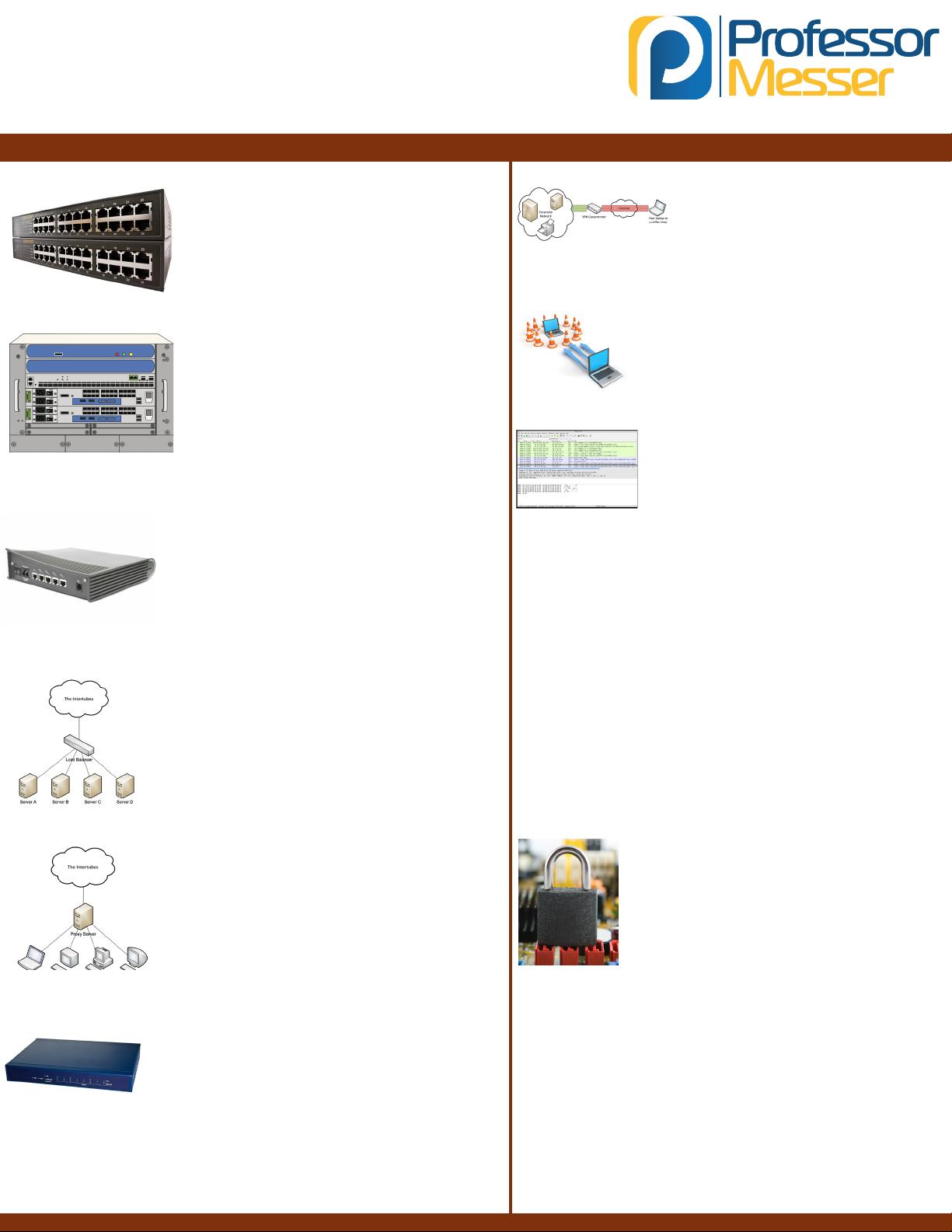
Network Devices
© 2014 Messer Studios, LLC
hp://www.ProfessorMesser.com
Professor Messer’s CompTIA SY0-401 Security+ Study Guide - Page 1
Switch
• An OSI layer 2 device
• Hardware bridging ASICs (very fast!)
• Forwards trac based on MAC address
• The core of an enterprise network
• High bandwidth - Many simultaneous packets
Router
• An OSI layer 3 device
• Routes trac between IP subnets
• Routers inside of switches are somemes
called “layer 3 switches”
• Layer 2 = Switch, Layer 3 = Router
• Oen connects diverse network types -
LAN, WAN, copper, ber
Firewall
• OSI layer 4 (TCP/UDP), some rewalls lter
through OSI layer 7
• Filters trac by port number
• Can encrypt trac into/out of the network
and between sites
• Can proxy trac - A common security technique
• Most rewalls can be layer 3 devices (routers)
Load balancer
• Distributes the load over many physical servers
• Very common in large environments
Proxy
• Sits between the users and the external network
• Receives the user requests and sends
the request on their behalf (the proxy)
• Applicaons may need to know how to
use the proxy (explicit)
• Some proxies are invisible (transparent)
All-in-one security appliance
• Unied Threat Management (UTM) /
Web security gateway
• URL lter / Content inspecon, malware
inspecon, spam lter, CSU/DSU, router, switch,
rewall, IDS/IPS, bandwidth shaper, VPN endpoint
VPN concentrator
• The connecon point
for remote users
• Trac is encrypted across the
Internet and decrypted on the
internal private network
Intrusion detecon/prevenon system
• Protects against OS and applicaon exploits
• Detecon
• Alerts but does not stop the aack
• Prevenon
• Blocks the aack
Protocol analyzer
• Captures network packets
• Decodes each part of the communicaon
• Sees all of the network conversaon
Spam Filters
• Stop unsolicited email at the gateway
• Whitelist
• Only receive email from trusted senders
• SMTP standards checking
• Block anything that doesn’t follow RFC standards
• rDNS - Reverse DNS
• Block email where the sender’s domain doesn’t match
the IP address
• Tarping
• Intenonally slow down the server conversaon
• Recipient ltering
• Block all email not addressed to a valid
recipient email address
Web Applicaon Firewall
• Applies rules to HTTP conversaons
• Allow or deny based on expected input
• Protects against exploits like SQL injecons
and buer overows
• Focus of Payment Card Industry Data
Security Standard (PCI DSS)
Applicaon-aware Security Devices
• Network-based Firewalls
• Control trac ows based on the applicaon
• Microso SQL Server, Twier, YouTube
• Intrusion Prevenon Systems
• Idenfy the applicaon
• Apply applicaon-specic vulnerability signatures
to the trac
• Host-based rewalls
• Work with the OS to determine the applicaon
Version 0x04
Network Administraon Principles
© 2014 Messer Studios, LLC
hp://www.ProfessorMesser.com
Professor Messer’s CompTIA SY0-401 Security+ Study Guide - Page 2
VLANs
Conguring rewall rules
• Allow or disallow trac based on security tuples
• Source IP, Desnaon IP, port number,
me of day, applicaon, etc.
• Evaluated top-to-boom
• There’s an implicit deny at the boom
VLANs
• Logically separate your switch ports into subnets
• VLANs cannot communicate to each
other without a router
• Group users together by funcon
Secure router conguraon
• Always change the default login / password
• Protect conguraon le transfers
• TFTP - in the clear
• SCP - encrypted
• HTTPS - encrypted
Access Control Lists (ACLs)
• Permissions associated with an object
• Used in le systems, network devices,
operang systems, and more
Switch port security
• IEEE 802.1X
• Port-based Network Access Control (PNAC)
• Makes extensive use of EAP and RADIUS
• Extensible Authencaon Protocol
• Remote Authencaon Dial In User Service
• Disable your unused ports
• Enable duplicate MAC address checking / spoong
Flood Guards
• Commonly seen on intrusion prevenon systems
• DoS / DDoS
• Denial of Service
• SYN oods
• Overload a server
• Ping oods / ping scans
• Overwhelm the network
• Idenfy what’s out there
• Port oods / port scans
• Idenfy open ports on a device
Spanning Tree Protocol (STP)
• IEEE standard 802.1D
• Prevents loops in bridged (switched) networks
• Built into the switch conguraon opons
Network Separaon
• Separate switches, separate routers, no overlap
• Used in sensive environments
• Logical separaon
• Virtualizaon of the network infrastructure
Log Analysis
• Good for post-event analysis
• Can provide useful real-me analysis
• Automaon and consolidaon is the key
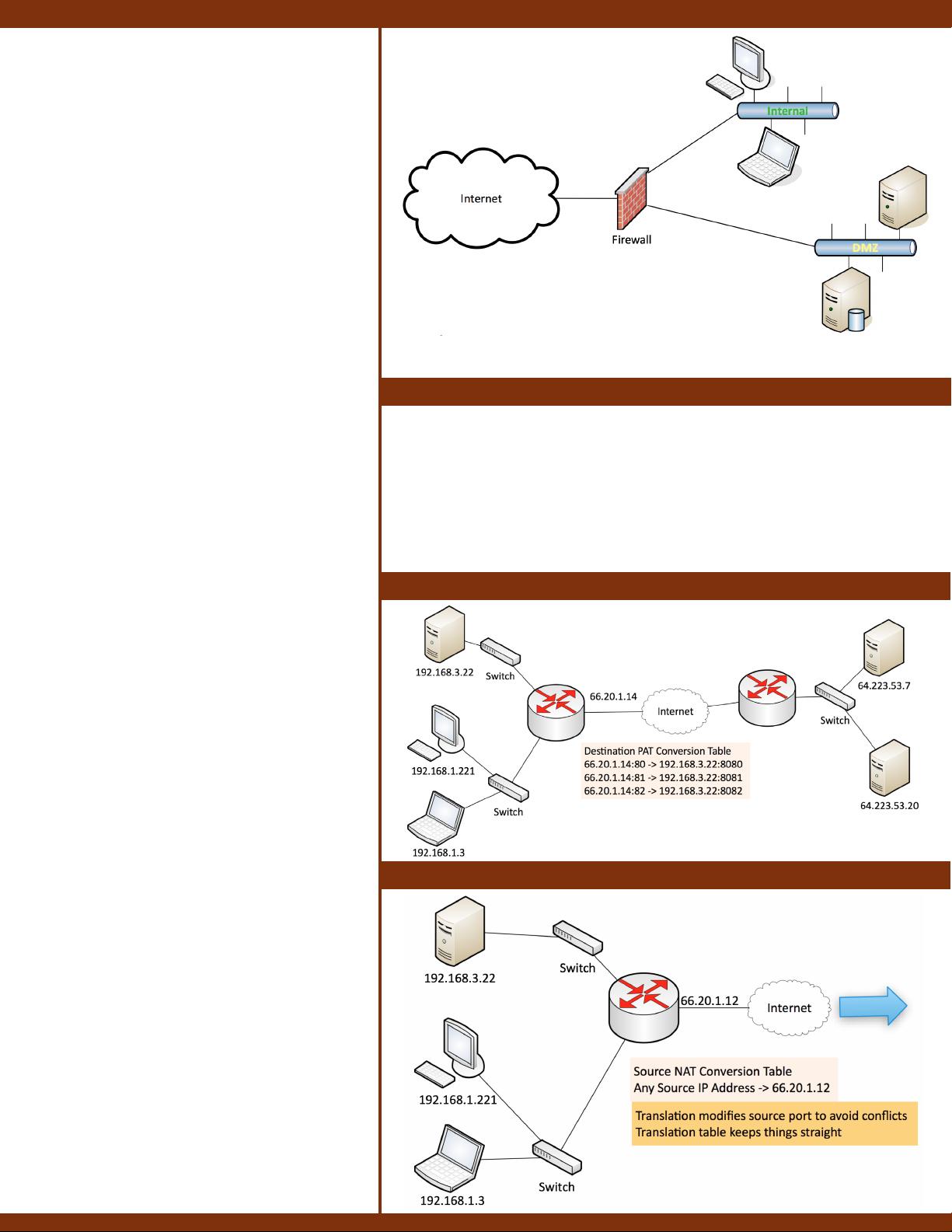
DMZ
DMZ (Demilitarized Zone)
• A layer of security between your internal network
and the Internet
• Protects external-facing services
• Usually less trusted than the Internal network connecon
• Logically separate your switch ports into subnets
• VLANs cannot communicate to each other without a router
• The router/rewall becomes the gatekeeper
• Control your organizaon’s trac from within
• Group users together by funcon
• Be careful not to separate users too far from their resources
• Is oen integrated with the NAC
• Move people automacally into their VLAN based on credenals
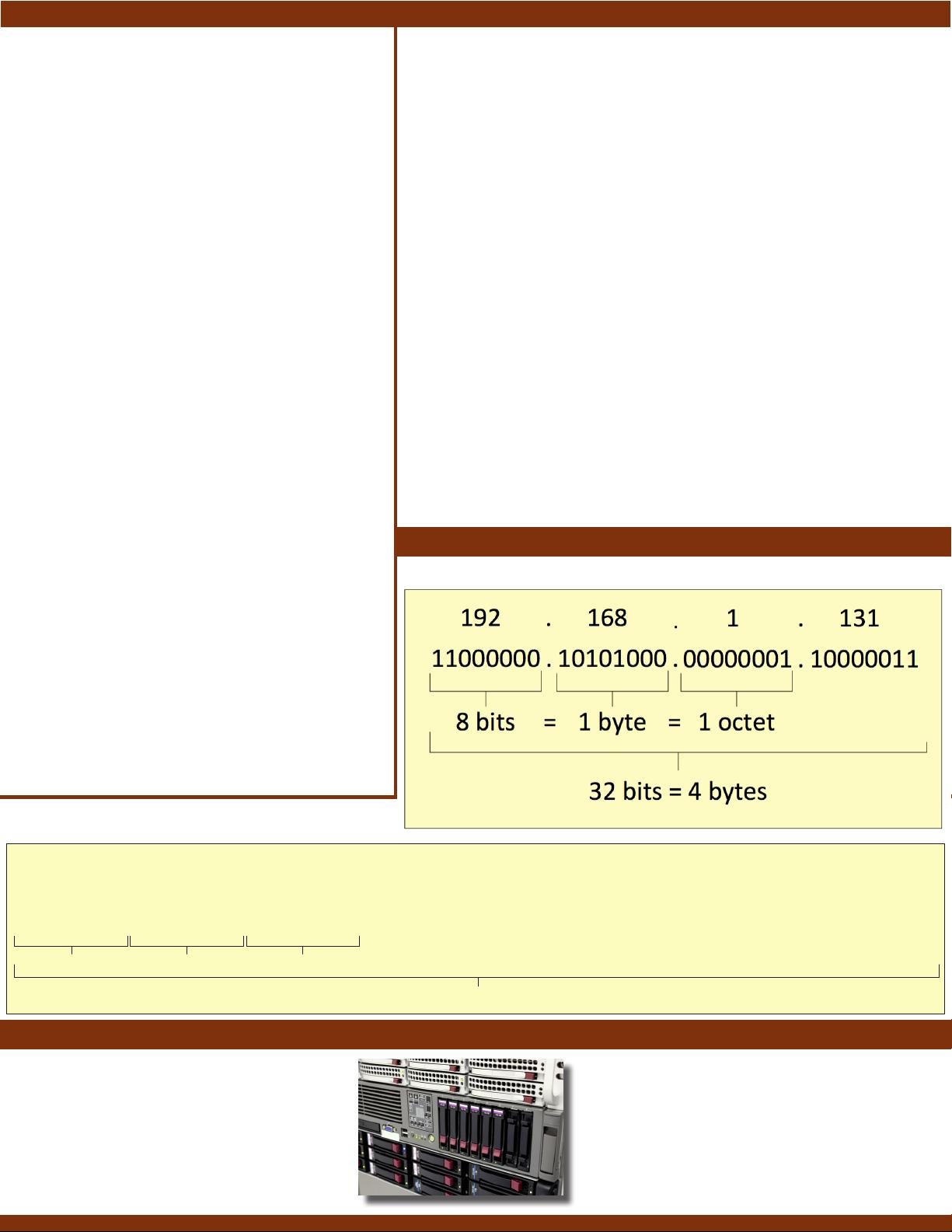
Stac NAT / Desnaon NAT
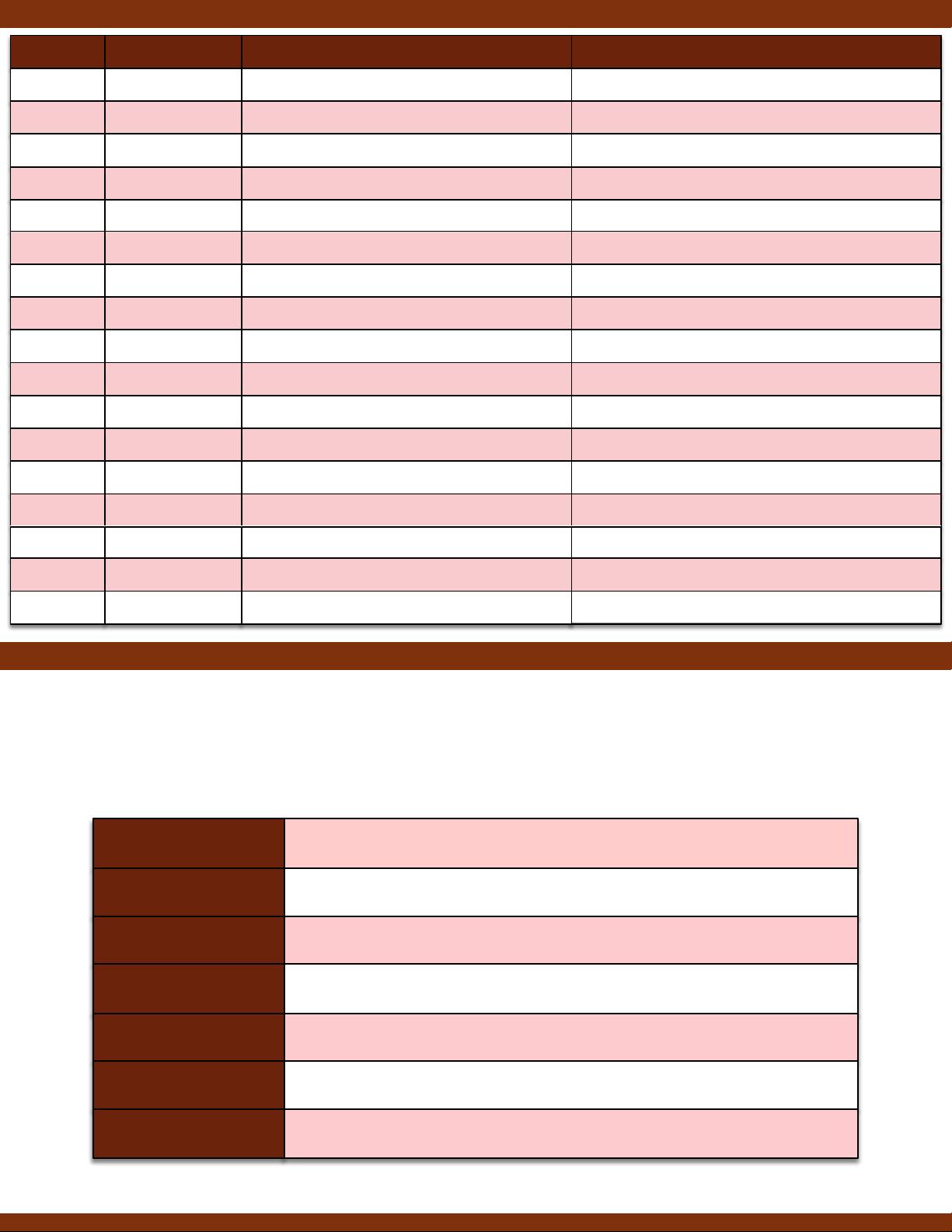
PAT (Port Address Translaon) / Source NAT
© 2014 Messer Studios, LLC
hp://www.ProfessorMesser.com
Professor Messer’s CompTIA SY0-401 Security+ Study Guide - Page 3
Network Design
Remote Access
• An important requirement
• We are increasingly mobile
• Take advantage of encrypon technologies
• Keep everything private
• Consider adding addional authencaon
technologies (One-me passwords)
• Constantly audit your access logs
Telephony
• One of the newest digital technologies
• And one of the most dicult to secure
• Firewalls generally don’t like VoIP technologies
• You’ll need protocol-specic applicaon gateways
• Don’t forget your legacy telephony!
• Long distance sll costs money
Network Access Control
• A complex technology
• But powerful when well engineered
• Very useful in large open environments
• Universies and large enterprises
• Requires a large security infrastructure
• Authencaon is crical
• Redundancy is required
Virtualizaon
• Huge cost savings
• Security has to catch up to the speed of change
• The control of physical objects is gone
• Also dicult to apply external security components
• Requires addional insight
• Harder to view intra-server communicaon
• Take advantage of your logs
• They’ll tell you much more than you can see
Defense in Depth
• Good security has many layers
• Firewall, DMZ, authencaon, intrusion detecon,
VPN access, an-virus and an-malware soware
Plaorm as a Service (PaaS)
• No servers, no soware, no maintenance team
• No hardware of any kind
• Someone else handles the plaorm, you handle the product
• You don’t have direct control of the data, people, or infrastructure
• SalesForce.com is an example of PaaS
Soware as a service (SaaS)
• On-demand soware, no local installaon
• Used for common business funcons such as payroll services
• Data and applicaons are centrally managed
• Gmail and Google Docs is an example of SaaS
Infrastructure as a service (IaaS)
• Somemes called Hardware as a Service (HaaS)
• Equipment is outsourced
• You are sll responsible for the overall device and applicaon management
• You’re also responsible for the security
• Your data is out there, but more within your control
• Web hosng and email services would be an example of IaaS
Cloud Deployment Models
• Private - A virtualized data center
• Public - Available to everyone over the Internet
• Hybrid - A mix of public and private
• Community - Several organizaons share the same resources
Cloud Compung
IPv4 and IPv6
IPv4 Addressing
fe80::5d18:652:cffd:8f52
fe80:0000:0000:0000:5d18:0652:cffd:8f52
fe80
1111111010000000
0000
0000000000000000
:
:
0000
0000000000000000
:
:
0000
0000000000000000
:
:
5d18
0101110100011000
:
:
0652
0000011001010010
:
:
cffd
1100111111111101
:
:
8f52
1000111101010010
:
:
16 bits 2 bytes=
128 bits = 16 bytes
2 octets=
IPv6 Addressing
Storage Area Networking
• Network Aached Storage (NAS)
• Connect to a shared storage device across
the network
• File-level access
• Storage Area Network (SAN)
• Looks and feels like a local storage device
• Block-level access
• Fibre Channel over Ethernet (FCoE)
• Run Fiber Channel on Ethernet, not routable
• Fibre Channel over IP (FCIP)
• Encapsulate Fibre Channel frames into IP
• iSCSI - Internet Small Computer Systems Interface
• Send SCSI commands over an IP network
© 2014 Messer Studios, LLC
hp://www.ProfessorMesser.com
Professor Messer’s CompTIA SY0-401 Security+ Study Guide - Page 4
Ports and Protocols
OSI Model
Protocol Descrip,onNamePort
DNS udp/53,+tcp/53 Convert+domain+names+to+IP+addressesDomain+Name+Services
SNMP udp/161 Gather+sta?s?cs+and+manage+network+devicesSimple+Network+Management+Protocol
Telnet tcp/23 Remote+console+login+to+network+devicesTelecommunica?on+Network
SSH tcp/22 Encrypted+console+loginSecure+Shell
FTP
TFTP
tcp/20,+tcp/21 Sends+and+receives+files+between+systems
udp/69 A+very+simple+file+transfer+applica?on
File+Transfer+Protocol
Trivial+File+Transfer+Protocol
HTTP tcp/80 Web+server+communica?onHypertext+Transfer+Protocol
HTTPS tcp/443
Web+server+communica?on+with+encryp?on
Hypertext+Transfer+Protocol+Secure
TLS/SSL tcp/443 Secure+protocols+for+web+browsing
Transport+Layer+Security+and+Secure+Sockets+Layer
SCP tcp/22 Rela?vely+simple+file+copy+over+SSHSecure+Copy
SFTP tcp/22 SSH+file+transfer+with+file+managementSecure+File+Transfer+Protocol
FTPS tcp/990,+tcp/989
Adds+security+to+FTP+with+TLS/SSL
FTP+over+SSL
NetBIOS
tcp/139
NetBIOS+over+TCP+X+Session+serviceNetwork+Basic+Input/Output+System
IPsec Various
Authen?ca?on,+integrity,+confiden?ality,+and+encryp?on
Internet+Protocol+Security
ICMP N/A
Management+protocol
Internet+Control+Message+Protocol
NetBIOS udp/137,+udp/138 NetBIOS+over+UDP+X+Name+service,+Datagram+serviceNetwork+Basic+Input/Output+System
IMAP tcp/143
Retrieve+and+store+email
Internet+Message+Access+Protocol
Layer&7&(&Applica.on The$layer$we$see$+$Google$Mail,$Twi2er,$Facebook
Encoding$and$encryp;on$(SSL$/$TLS)
UDP
Layer&6&(&Presenta.on
Layer&5&(&Session
Layer&4&(&Transport
Layer&3&(&Network
Layer&2&(&Data&Link
Layer&1&(&Physical
Communica;on$between$devices$(control$protocols,$tunneling$protocols)
The$"post$office"$layer$(TCP$segments,$UDP$datagrams)
The$rou;ng$layer$(IP$addresses,$routers,$packets)
The$switching$layer$(frames,$MAC$addresses,$EUI+48,$EUI+64,$switches)
Signaling,$cabling,$connectors$(cables,$NICs,$hubs)
OSI Mnemonics
• Please Do Not Trust Sales Person’s Answers
• All People Seem To Need Data Processing
• Please Do Not Throw Sausage Pizza Away!
© 2014 Messer Studios, LLC
hp://www.ProfessorMesser.com
Professor Messer’s CompTIA SY0-401 Security+ Study Guide - Page 5
Wireless Encrypon and Authencaon
WEP
• 64-bit or 128-bit key size
• Cryptographic vulnerabiles found in 2001
• WEP is no longer used
WPA
• Short-term workaround aer WEP
• Used RC4 cipher as a TKIP (Temporal Key Integrity Protocol)
• TKIP has its own vulnerabilies
WPA2
• Replaced TKIP with CCMP (Counter Mode with Cipher Block Chaining
Message Authencaon Code Protocol)
• Replaced RC4 with AES (Advanced Encrypon Standard)
• WPA2 is the latest and most secure wireless encrypon method
WPA2-Enterprise
• WPA2-Enterprise adds 802.1x
• RADIUS server authencaon
EAP (Extensible Authencaon Protocol)
• An authencaon framework
• WPA and WPA2 use ve EAP types as
authencaon mechanisms
LEAP (Lightweight Extensible Authencaon Protocol)
• Cisco proprietary
• Uses passwords only
• No detailed cercate management
• Based on MS-CHAP
(including MS-CHAP security shortcomings)
PEAP (Protected Extensible Authencaon Protocol)
• Created by Cisco, Microso, and RSA Security
• Encapsulates EAP in a TLS tunnel
• Only one cercate needed, on the server
MAC (Media Access Control) ltering
• Access is controlled through the physical hardware address
• It’s easy to nd a working MAC addresses through wireless LAN analysis
• MAC addresses can be spoofed
• Security through obscurity
SSID (Service Set Idener) Management
• The SSID is the name of the wireless network
• i.e., LINKSYS, DEFAULT, NETGEAR
• Change the SSID to something appropriate for its use
• The SSID broadcasts can be disabled
• You can sll determine the SSID through wireless network analysis
• Security through obscurity
Temporal Key Integrity Protocol
• Created when WEP was broken
• We needed a stopgap to make 802.11 stronger
• Mixed the keys - Combines the secret root key with the IV
• Adds sequence counter - Prevents replay aacks
• 64-bit Message Integrity Check - Protects against tampering
• Used in WPA (Wi-Fi Protected Access) prior to the creaon of WPA2
CCMP
• Counter Mode with Cipher Block Chaining
Message Authencaon Code Protocol
• Replaced TKIP when WPA2 was published
• A more advanced security protocol
• Based on AES and uses a 128-bit key and a 128-bit block size
• Requires addional compung resources
• Data condenality - Only authorized pares can access the informaon
• Authencaon - Provides proof of genuineness of the user
• Access control - Allow or disallow access to the network
Site Surveys
• Sample the exisng wireless spectrum
• Idenfy exisng access points
• Work around exisng frequencies - layout and plan for interference
• Plan for ongoing site surveys - things will certainly change
VPN over Wireless Networks
• Wireless from your local coee shop - no encrypon
• Everyone around the coee shop can see your trac
• Exceponally easy to capture your data
• Some of your data might be encrypted with HTTPS. Maybe.
• Protect all of your trac with a VPN tunnel
Capve Portal
• Authencaon to a network
• Common on wireless networks
• Access table recognizes a lack of authencaon
• Redirects your web access to a capve portal page
• Username / password
• And addional authencaon factors
• Once proper authencaon is provided,
the web session connues
• Unl the capve portal removes your access
Wireless Security
Omnidireconal Antennas
• One of the most common
• Included on most access points
• Signal is evenly distributed on all sides
• Omni=all
• Good choice for most environments
• You need coverage in all direcons
• No ability to focus the signal
• A dierent antenna will be required
Direconal Antennas
• Focus the signal - Increased distances
• Send and receive in a single direcon
• Focused transmission and listening
• Antenna performance is measured in dB
• Double power every 3dB of gain
• Yagi antenna - Very direconal and high gain
• Parabolic antenna - Focus the signal to a single point
剩余35页未读,继续阅读
资源评论

fengxingtianxia7
- 粉丝: 0
- 资源: 1
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
