没有合适的资源?快使用搜索试试~ 我知道了~
资源详情
资源评论
资源推荐

Choosing a Primary Key: Natural or Surrogate?
This article overviews strategies for assigning primary keys to a table within a relational database. In particular, it focuses on the issue of when to use natural
keys and when to use surrogate keys. Some people will tell you that you should always use natural keys and others will tell you that you should always use
surrogate keys. These people invariably prove to be wrong, typically they're doing little more than sharing the prejudices of their "data religion" with you. The
reality is that natural and surrogate keys each have their advantages and disadvantages, and that no strategy is perfect for all situations. In other words, you
need to know what you're doing if you want to get it right. This article discusses:
Common key terminology
Strategies for assigning keys
Surrogate key implementation strategies
Tips for eective keys
What to do when you make the "wrong" choice
1. Common Key Terminology
Let's start by describing some common terminology pertaining to keys and then work through an example. These terms are:
Key. A key is one or more data attributes that uniquely identify an entity. In a physical database a key would be formed of one or more table columns
whose value(s) uniquely identifies a row within a relational table.
Composite key. A key that is composed of two or more attributes.
Natural key. A key that is formed of attributes that already exist in the real world. For example, U.S. citizens are issued a Social Security Number
(SSN) that is unique to them (this isn't guaranteed to be true, but it's pretty darn close in practice). SSN could be used as a natural key, assuming
privacy laws allow it, for a Person entity (assuming the scope of your organization is limited to the U.S.).

Surrogate key. A key with no business meaning.
Candidate key. An entity type in a logical data model will have zero or more candidate keys, also referred to simply as unique identifiers (note: some
people don't believe in identifying candidate keys in LDMs, so there's no hard and fast rules). For example, if we only interact with American citizens
then SSN is one candidate key for the Person entity type and the combination of name and phone number (assuming the combination is unique) is
potentially a second candidate key. Both of these keys are called candidate keys because they are candidates to be chosen as the primary key, an
alternate key or perhaps not even a key at all within a physical data model.
Primary key. The preferred key for an entity type.
Alternate key. Also known as a secondary key, is another unique identifier of a row within a table.
Foreign key. One or more attributes in an entity type that represents a key, either primary or secondary, in another entity type.
Figure 1 presents a physical data model (PDM) for a physical address using the UML notation. In Figure 1 the Customer table has the CustomerNumber
column as its primary key and SocialSecurityNumber as an alternate key. This indicates that the preferred way to access customer information is through the
value of a person’s customer number although your software can get at the same information if it has the person’s social security number. The
CustomerHasAddress table has a composite primary key, the combination of CustomerNumber and AddressID . A foreign key is one or more attributes in an
entity type that represents a key, either primary or secondary, in another entity type. Foreign keys are used to maintain relationships between rows. For
example, the relationships between rows in the CustomerHasAddress table and the Customer table is maintained by the CustomerNumber column within the
CustomerHasAddress table. The interesting thing about the CustomerNumber column is the fact that it is part of the primary key for CustomerHasAddress as
well as the foreign key to the Customer table. Similarly, the AddressID column is part of the primary key of CustomerHasAddress as well as a foreign key to
the Address table to maintain the relationship with rows of Address.
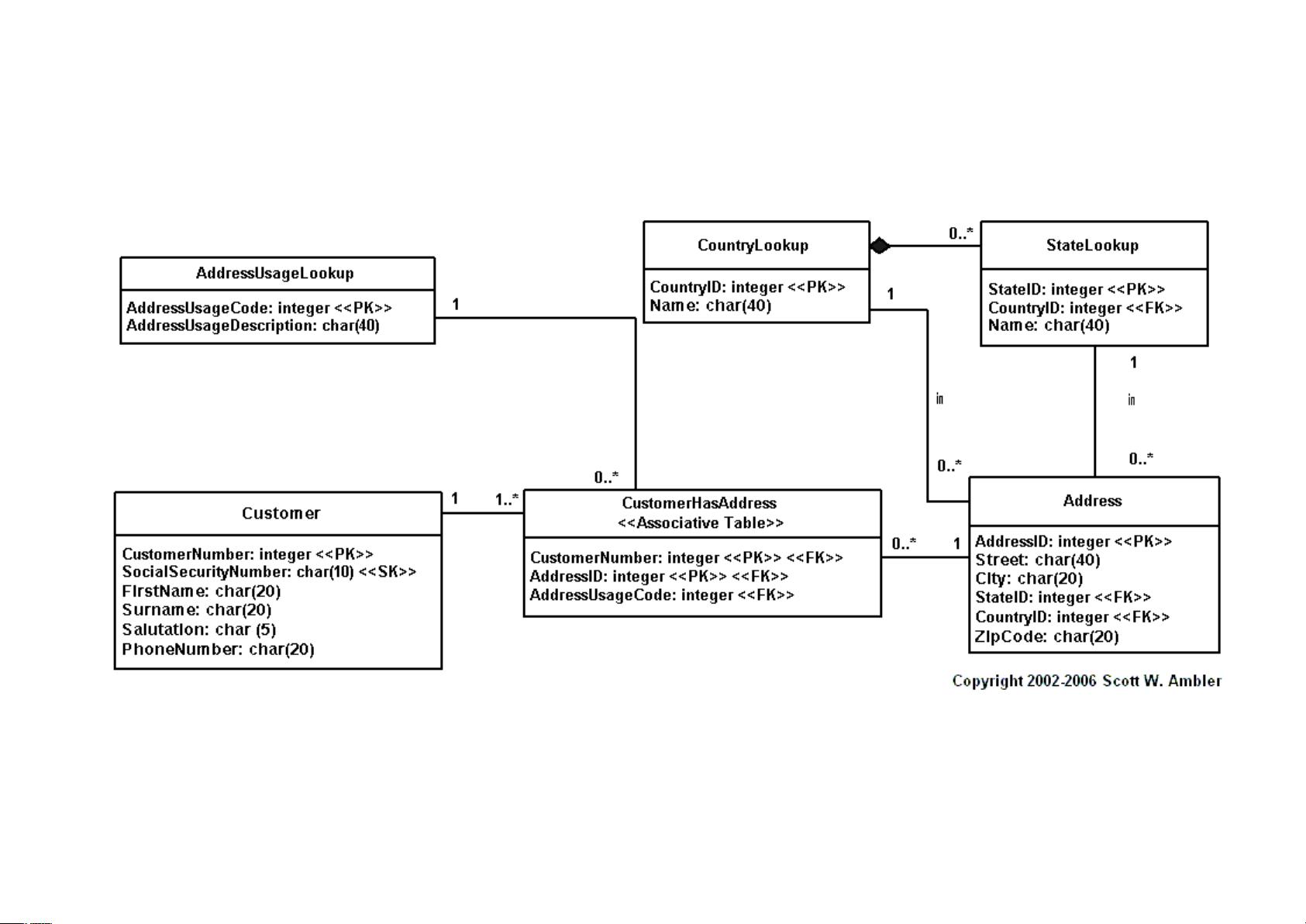
Figure 1. A simple PDM modeling Customer and Address.
剩余11页未读,继续阅读
bjmlml
- 粉丝: 0
- 资源: 11
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- C#,煎饼排序问题(Pancake Sorting Problem)算法与源代码
- C#,排列组合的堆生成法(Heap’s Algorithm for generating permutations)算法与源代码
- C#,老鼠迷宫问题的回溯法求解(Rat in a Maze)算法与源代码
- 6693eeb8d683458a07938615fba9e68f.apk
- C#,数值计算,解微分方程的龙格-库塔二阶方法与源代码
- C#,数值计算,用割线法(Secant Method)求方程根的算法与源代码
- C#,子集和问题(Subset Sum Problem)的算法与源代码
- mongodb 数据库基本操作
- Linux操作系统基础教程
- Linux操作系统相关习题集
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论0