
© Open Systems Solutions 1999
ASN.1 Complete
by
Prof John Larmouth
2 © OSS,31 May 1999
Dedication
This book is dedicated to the girls at Withington Girls' School that are there with my daughter
Sarah-Jayne and to the boys at The Manchester Grammar School that are there with my son
James, in the hope that it may some day be of use to some of them!

© OS, 31 May 1999 3
Contents
Contents 3
Foreword 13
Introduction 15
1 The global communications infrastructure 15
2 What exactly is ASN.1? 16
3 The development process with ASN.1 18
4 Structure of the text. 18
SECTION I ASN.1 OVERVIEW 21
Chapter 1 Specification of protocols 22
1 What is a protocol? 22
2 Protocol specification - some basic concepts 24
2.1 Layering and protocol "holes" 25
2.2 Early developments of layering 26
2.3 The disadvantages of layering - keep it simple! 28
2.4 Extensibility 28
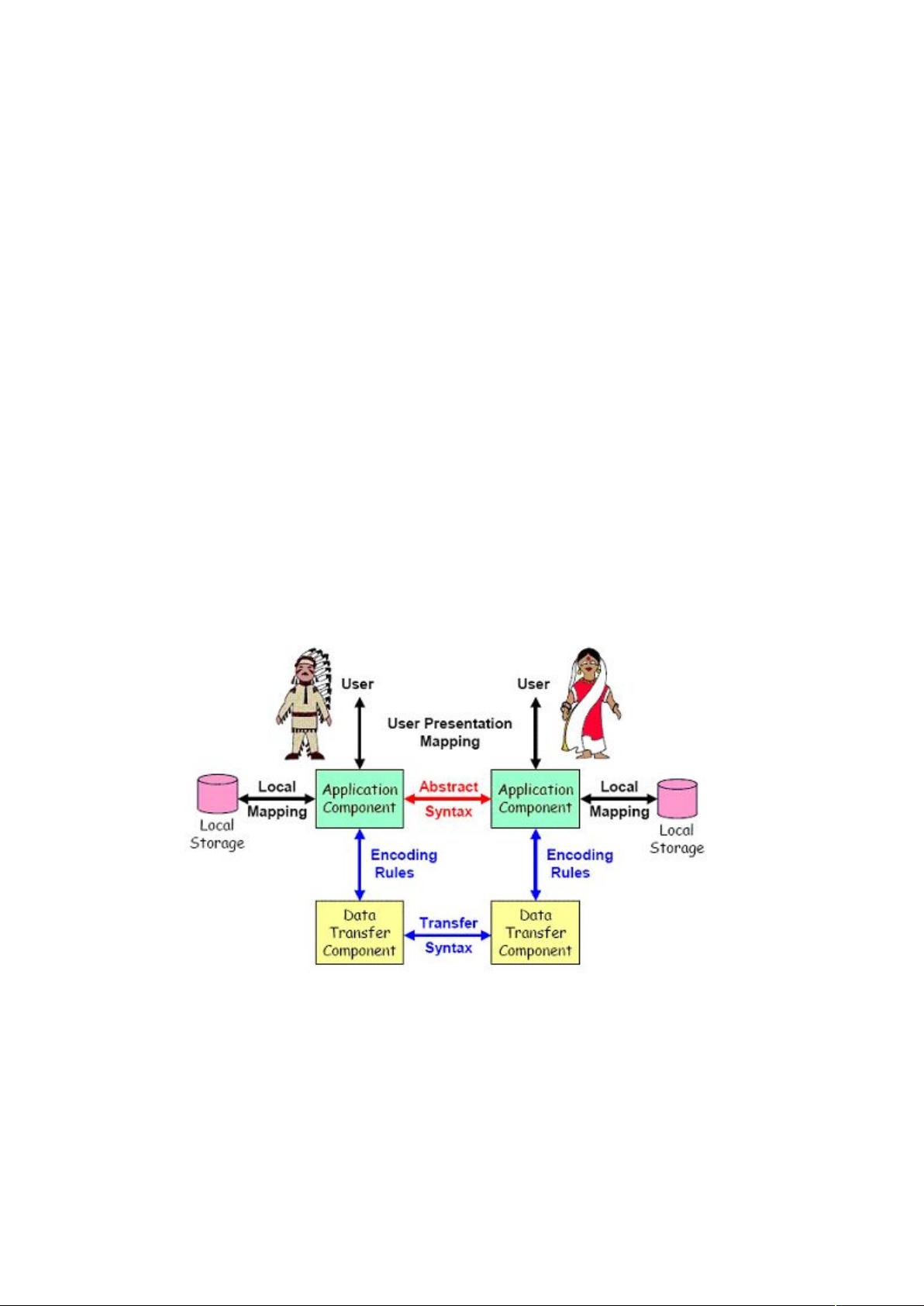
2.5 Abstract and transfer syntax 30
2.6 Command line or statement-based approaches 32
2.7 Use of an Interface Definition Language 32
3 More on abstract and transfer syntaxes 32
3.1 Abstract values and types 32
3.2 Encoding abstract values 33
4 Evaluative discussion 35
4.1 There are many ways of skinning a cat - does it matter? 35
4.2 Early work with multiple transfer syntaxes 35
4.3 Benefits 36
Efficient use of local representations 36
Improved representations over time 36
Reuse of encoding schemes 36
Structuring of code 37
Reuse of code and common tools 38
Testing and line monitor tools 38
Multiple documents requires "glue" 38
The "tools" business 39
5 Protocol specification and implementation - a series of case studies 39
5.1 Octet sequences and fields within octets 39
5.2 The TLV approach 40
5.3 The EDIFACT graphical syntax 41
5.4 Use of BNF to specify a character-based syntax 42
5.5 Specification and implementation using ASN.1 - early 1980s 43
5.6 Specification and implementation using ASN.1 - 1990’s 44
Chapter 2 Introduction to ASN.1 47

4 © OSS,31 May 1999
1 Introduction 47
2 The example 48
2.1 The top-level type 49
2.2 Bold is what matters! 49
2.3 Names in italics are used to tie things together 49
2.4 Names in normal font are the names of fields/elements/items 50
2.5 Back to the example! 50
2.6 The BranchIdentification type 52
2.7 Those tags 54
3 Getting rid of the different fonts 55
4 Tying up some lose ends 56
4.1 Summary of type and value assignments 56
4.2 The form of names 57
4.3 Layout and comment 57
5 So what else do you need to know? 58
Chapter 3 Structuring an ASN.1 specification 60
1 An example 61
2 Publication style for ASN.1 specifications 62
2.1 Use of line-numbers. 63
2.2 Duplicating the ASN.1 text 64
2.3 Providing machine-readable copy 64
3 Returning to the module header! 65
3.1 Syntactic discussion 65
3.2 The tagging environment 67
3.2.1 An environment of explicit tagging 68
3.2.2 An environment of implicit tagging 68
3.2.3 An environment of automatic tagging 68
3.3 The extensibility environment 69
4 Exports/imports statements 71
5 Refining our structure 73
6 Complete specifications 76
7 Conclusion 77
Chapter 4 The basic data types and construction mechanisms - closure 78
1 Illustration by example 79
2 Discussion of the built-in types 80
2.1 The BOOLEAN type 80
2.2 The INTEGER type 80
2.3 The ENUMERATED type 82
2.4 The REAL type 83
2.5 The BIT STRING type 84
2.6 The OCTET STRING type 87
2.7 The NULL type 88
2.8 Some character string types 88
2.9 The OBJECT IDENTIFIER type 89
2.10 The ObjectDescriptor type 90
2.11 The two ASN.1 date/time types 91
3 Additional notational constructs 93
3.1 The selection-type notation 93
3.2 The COMPONENTS OF notation 94
3.3 SEQUENCE or SET? 95
3.4 SEQUENCE, SET, and CHOICE (etc) value-notation 96
4 What else is in X.680/ISO 8824-1? 97

© OS, 31 May 1999 5
Chapter 5 Reference to more complex areas 99
1 Object identifiers 100
2 Character string types 100
3 Subtyping 102
4 Tagging 103
5 Extensibility, exceptions and version brackets 104
6 Hole types 105
7 Macros 106
8 Information object classes and objects and object sets 107
9 Other types of constraints 108
10 Parameterization 108
12 The ASN.1 semantic model 109
13 Conclusion 109
Chapter 6 Using an ASN.1 compiler 110
1 The route to an implementation 110
2 What is an ASN.1 compiler? 111
3 The overall features of an ASN.1-compiler-tool 113
4 Use of a simple library of encode/decode routines 113
4.1 Encoding 114
4.2 Decoding 115
5 Using an ASN.1-compiler-tool 116
5.1 Basic considerations 116
5.2 What do tool designers have to decide? 116
5.3 The mapping to a programming-language data structure 117
5.4 Memory and CPU trade-offs at run-time 118
5.5 Control of a tool 119
6 Use of the "OSS ASN.1 Tools" product 120
7 What makes one ASN.1-comiler-tool better than another? 121
8 Conclusion 122
Chapter 7 Management and design issues for ASN.1 specification and implementation 123
1 Global issues for management decisions 124
1.1 Specification 124
1.1.1 To use ASN.1 or not! 124
1.1.2 To copy or not? 124
1.2 Implementation - setting the budget 125
1.2.1 Getting the specs 125
1.2.2 Training courses, tutorials, and consultants 126
1.3 Implementation platform and tools 126
2 Issues for specifiers 127
2.1 Guiding principles 127
2.2 Decisions on style 128
2.3 Your top-level type 128
2.4 Integer sizes and bounds 129
2.5 Extensibility issues 130
2.6 Exception handling 131
2.6.1 The requirement 131
2.6.2 Common forms of exception handling 131
2.6.2.1 SEQUENCE and SET 131
2.6.2.2 CHOICE 131
2.6.2.3 INTEGER and ENUMERATED 132
2.6.2.4 Extensible strings 132
2.6.2.5 Extensible bounds on SET OF and SEQUENCE OF 132

















- 1
- 2
前往页