没有合适的资源?快使用搜索试试~ 我知道了~
netflow协议详解,内部包含netflow协议分析,netflow数据包分析等
资源推荐
资源详情
资源评论

White Paper
© 2006, 2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 1 of 21
Introduction to Cisco IOS
®
Flexible NetFlow
Last updated: September 2008
The next-generation in flow technology allowing optimization of the network infrastructure,
reducing operation costs, improving capacity planning and security incident detection with
increased flexibility and scalability.
Introduction
NetFlow invented by Cisco has become the standard for acquiring IP operational data for many
customers. Visibility into the network is an indispensable tool. In response to new requirements
and pressures, network operators are finding it critical to understand how the network is behaving
including:
●
Application and network usage
●
Understand who, what, when, where, and how network traffic is flowing
●
Network efficiency and utilization of network resources
●
The impact of changes to the network
●
Network anomaly and security vulnerabilities
●
Long term compliance, business process and audit trail
Applications for NetFlow data are constantly being invented but the key usages include:
●
Real-time network monitoring
●
Application and user profiling
●
Network planning and capacity planning
●
Security incident detection and classification
●
Accounting and billing
●
Network data warehousing, forensics and data mining
●
Troubleshooting
NetFlow Based Network Awareness
The ability to characterize IP traffic and understand who sent it, the traffic destination, the time of
day, the application information, is critical for network availability, performance and
troubleshooting. Monitoring IP traffic flows facilitates more accurate capacity planning and ensures
that resources are used appropriately in support of organizational goals. It helps Cisco customers
determine how to optimize resource usage, plan network capacity, where to apply Quality of
Service (QoS) and it plays a vital role in network security to detect Denial–of–Service (DoS)
attacks and network-propagated worms.
NetFlow facilitates solutions to many common problems encountered by network professionals as
shown in Table 1.
Table 1. Common Solutions Facilitated by NetFlow

White Paper
© 2006, 2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 2 of 21
NetFlow Facilities Solutions To: Description
Analyze new applications and their
network impact
Identify new application network load such as VoIP or remote site additions.
Reduction in peak WAN traffic Use NetFlow statistics to measure WAN traffic improvement from application-
policy changes; understand who is utilizing the network and the network top
talkers.
Troubleshooting and understanding
network pain points
Diagnose slow network performance, bandwidth hogs and bandwidth utilization in
real-time with command line interface or reporting tools.
Detection of unauthorized WAN traffic Avoid costly upgrades by identifying the applications causing congestion.
Security and anomaly detection NetFlow can be used for anomaly detection, worm diagnosis along with
applications.
Validation of QoS parameters Confirm that appropriate bandwidth has been allocated to each Class of Service
(CoS) and that no CoS is over- or under-subscribed.
For a primer in the basics of NetFlow please read the
“Introduction to NetFlow—A Technical
Overview” document first.
The Next Generation in Flow Technology—Flexible NetFlow
Cisco is now innovating flow technology to a new level beyond what has been traditionally
available. Cisco IOS Flexible NetFlow is Cisco’s next-generation flow technology. Flexible NetFlow
provides enhanced optimization of the network infrastructure, reduces costs, and improves
capacity planning and security detection beyond other flow based technologies available today.
Key Advantages to using Flexible NetFlow:
●
Flexibility, scalability, aggregation of flow data beyond traditional NetFlow
●
The ability to monitor a wider range of packet information producing new information about
network behavior
●
Enhanced network anomaly and security detection
●
User configurable flow information to perform customized traffic identification and the ability
to focus and monitor specific network behavior
●
Convergence of multiple accounting technologies into one accounting mechanism
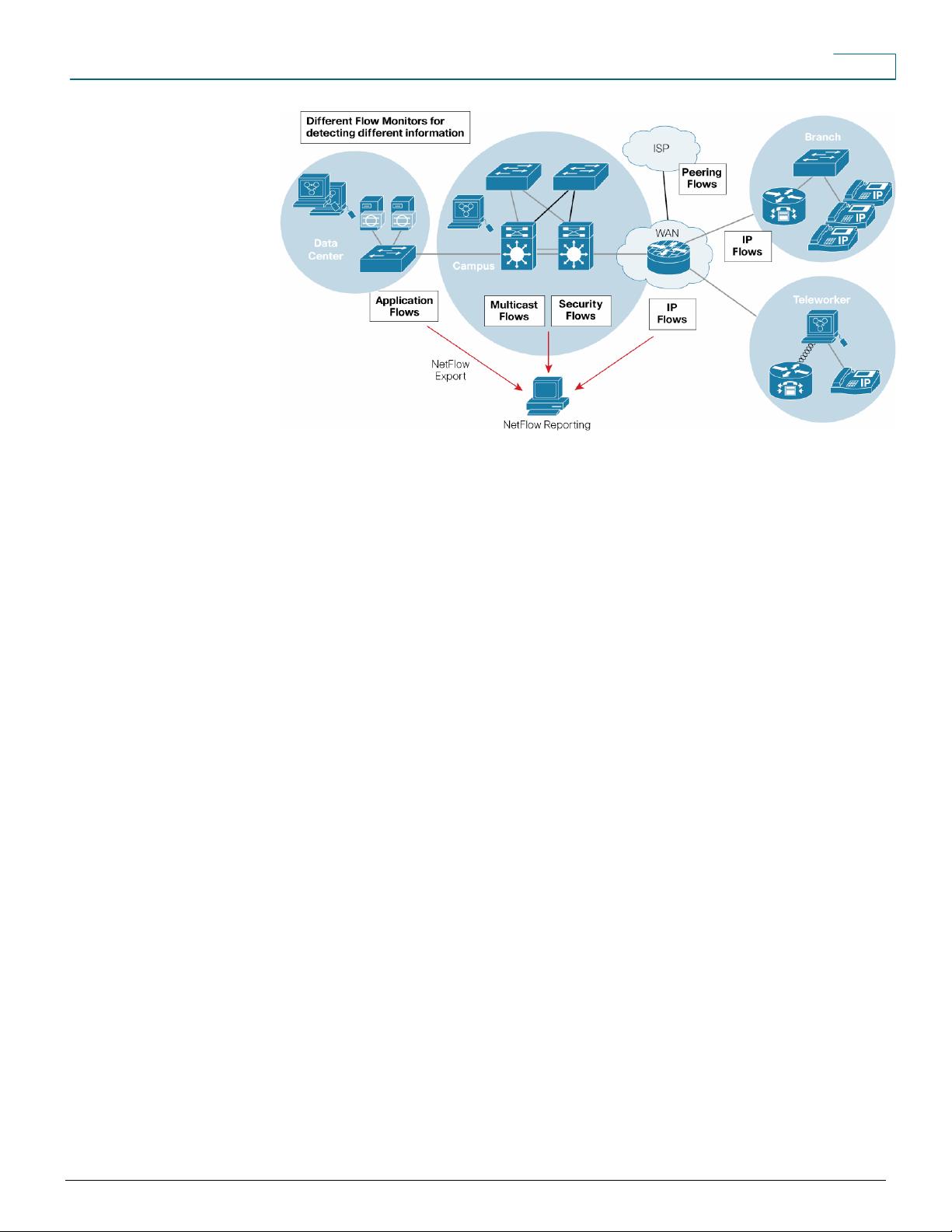
It provides a NetFlow architecture that can track multiple NetFlow applications simultaneously. For
example, the user can create simultaneous and separate Flow Monitors for security analysis and
traffic analysis. Cisco IOS Flexible NetFlow provides enhanced security detection and or network
troubleshooting by allowing customization of flow information. For example, the user can create a
specific Flow Monitor to focus and analyze a particular network issue or incident. It provides real-
time monitoring with immediate flow cache capabilities and long term or permanent tracking of flow
data. Cisco IOS Flexible NetFlow will enhance NetFlow’s already rich feature capabilities allowing
the tracking of information at layer 2 for switching environments, layer 3 and 4 for IP information
and up to layer 7 with deep packet inspection for application monitoring. Figure 1 shows various
types of Flow Monitors to view and understand network behavior.
Figure 1. Example of Flexible NetFlow Customizable Flow Monitors
White Paper
© 2006, 2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 3 of 21
An Example of Application Tracking with Flexible NetFlow
Flexible NetFlow unlike traditional NetFlow allows the user to customize and focus on specific
network information. Scalability of the NetFlow analysis is optimized and Flexible NetFlow gives
the opportunity to track the important information for the organization. By targeting specific
information the amount of information will be reduced and the number of flows being exported
reduced, allowing enhanced scalability and aggregation. If for instance the user was interested in
TCP application analysis, in Flexible NetFlow the user would configure the tracking of the NetFlow
field’s source and destination IP addresses, TCP source and destination ports and NetFlow will
examine the packets for this information. This information will effectively show who is sending and
receiving the traffic per application port. In traditional NetFlow, packet information is used to create
flows but this information is fixed and not configurable by the user. In traditional NetFlow
aggregation comes with the expense of lost information but in Flexible NetFlow the user can
actually track multiple sets of information to make sure all flow information in the network is
captured efficiently. In the above example the user only needs four NetFlow fields to track
application usage and this is contrasted to 7 fields in traditional NetFlow. In traditional NetFlow, the
user must track the 7 key fields and each field tracked leads to a greater number of flows.
An Example of Security Detection with Flexible Netflow
Flexible NetFlow is an excellent attack detection tool with capabilities to track all parts of the IPv4
header and even packet sections, and characterize this information into flows. It is expected that
security detection systems will listen to NetFlow data and upon finding an issue in the network,
create a virtual bucket or virtual cache that will be configured to track specific information and
pinpoint details about the attack pattern or worm propagation. The capability to create caches on
the fly with specific information combined with input filtering (ie: filtering all flows to a specific
destination) allows Flexible NetFlow to be a better security detection tool than current flow
technologies. It is expected common attacks such as port scans for worm target discovery and
worm propagation will be tracked in Flexible NetFlow. Let’s discuss a common simpler attack, in
which TCP flags are used to flood open TCP requests to a destination server (ie: SYN flood
attack). The attacking device will send a stream TCP SYN’s to a given destination address but
never send the ACK in response to the servers SYN-ACK as part of the TCP 3-way handshake.
The flow information needed for security monitor requires the tracking of three key fields:
destination address or subnet, TCP flags and packet count. The security device may be monitoring

White Paper
© 2006, 2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 4 of 21
general NetFlow information and this data may trigger a detailed view of this particular attack. The
detailed Flow Monitor might include input filtering to limit what traffic is visible in the NetFlow cache
along with the tracking of the specific information to diagnose the TCP based attack. In this case,
the user may want to filter all flow information to the server destination address or subnet to limit
the amount of information the security server needs to evaluate. If the security detection server
decided it understood this attack, it might then program another virtual cache or bucket to export
payload information or sections of packets to take a deeper look at a signature within the packet.
The above is just one of many possible examples of how Flexible NetFlow can be used to detect
security incidents.
What are the Key Components Within Flexible Netflow?
NetFlow has a number of key components:
●
NetFlow cache
●
NetFlow Flow Record
●
Flow export timers
●
NetFlow export format
●
NetFlow server for collection and reporting
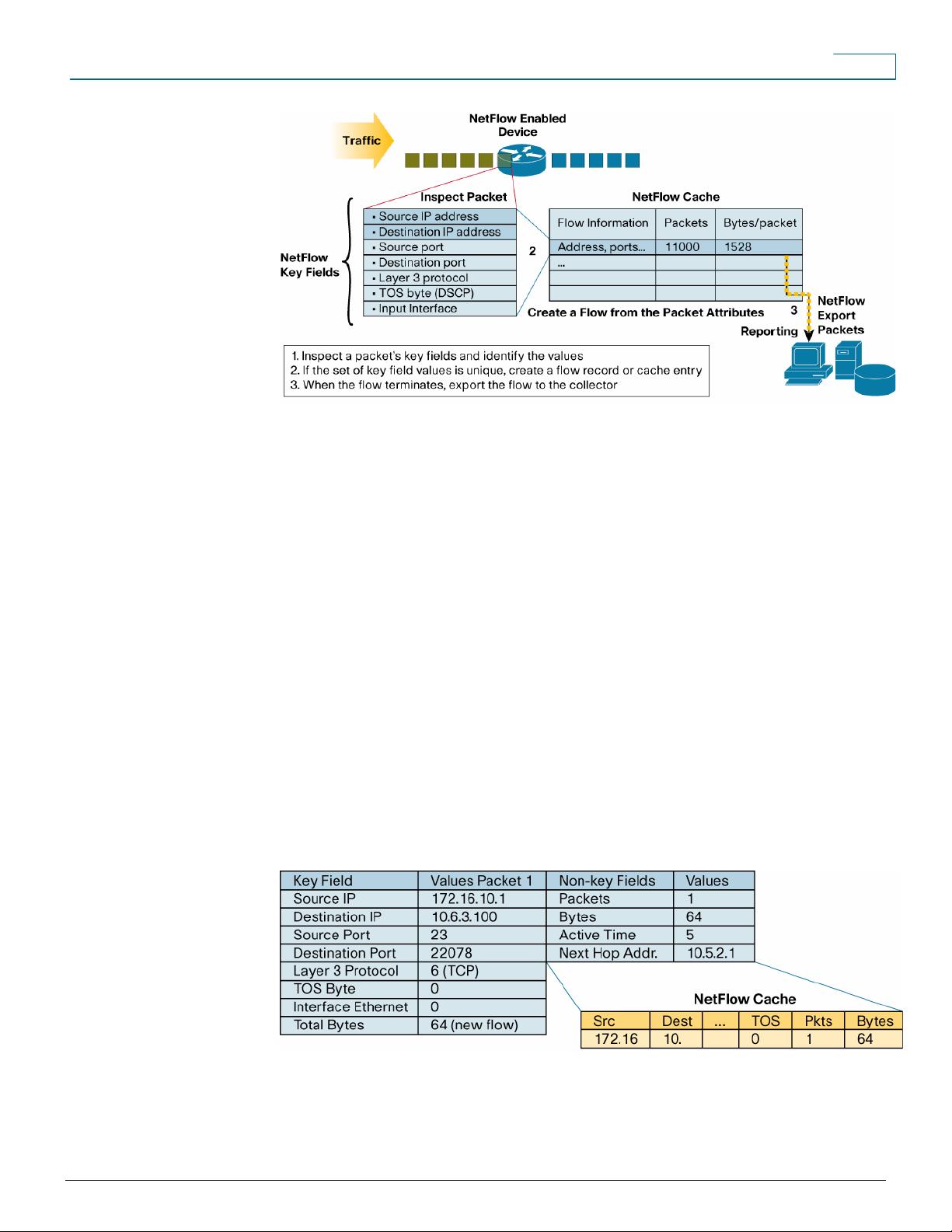
The NetFlow cache stores flow information. The Flow Record is created by inspecting a packet
and a description of packet information is added to the NetFlow cache as the Flow Record.
NetFlow exports or pushes flow information to the NetFlow reporting server. This is in contrast to
SNMP pull or the polling model to retrieve data. The Flow Records in the cache will expire or
terminate and be exported to a NetFlow collector and be used to create management reports. The
flows will expire based on timers and if the flow is inactive (no new packets and bytes for the flow)
it will be exported. Flow timers are discussed later in the document.
What is a Flexible NetFlow Key Field?
Each packet that is forwarded within a router or switch is examined for a set of IP packet attributes.
These attributes are the IP packet identity or key fields for the flow and determine if the packet
information is unique or similar to other packets.
Traditionally, an IP flow is based on a set of seven IP packet attributes. This set of key fields is
tracked and if the set of values for these fields are unique, a new Flow Record is created in the
NetFlow cache.
All packets with the same source/destination IP address, source/destination ports, protocol,
interface and class of service are grouped into a flow and then packets and bytes tallied. This
methodology of flow characterization or determining a flow is scalable because a large amount of
network information is condensed into a database of NetFlow information called the NetFlow
cache. The NetFlow cache is associated with a flexible Flow Monitor capability that will be
discussed in more detail within this document. Figure 2 shows the basic components of NetFlow
including the flow key fields, NetFlow cache and reporting server.
Figure 2. Creating a Flow in the NetFlow Cache
White Paper
© 2006, 2008 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 5 of 21
What is a Flexible NetFlow Non-Key Field?
Additional information can be added to the Flow Record and this information is named non-key
fields. Non-key fields are added to the flow entry in the NetFlow cache and exported. The non-key
fields are not used to create or characterize the flows but are exported and just added to the flow.
In Flexible NetFlow, non-key fields are also configurable by the user. If a field is non-key, normally
only the first packet of the flow is used for the value in this field.
Typical non-key NetFlow fields include:
●
Flow timestamps to understand the life of a flow; timestamps are useful for calculating
packets and bytes per second
●
Next hop IP addresses including BGP routing Autonomous Systems (AS)
●
Subnet mask for the source and destination addresses to calculate prefixes
●
TCP flags to examine TCP handshakes
Creating a Flow with Key and Non-key Fields
Figure 3 is an example of flow creation based on NetFlow key and non-key fields. The first packet
is inspected and the key field values are found and the set of key field values is unique within the
flow cache and a flow is created.
Figure 3. Packet 1 has Key and Non-Key Field Values in the Netflow Cache
Packet 2 is then inspected and the values of the key fields are the same as packet 1 and not
unique, so packets and bytes are incremented for the existing flow. Figure 4 shows how the
packets and bytes are incremented for the flow.
剩余20页未读,继续阅读
资源评论

sebastianchris
- 粉丝: 0
- 资源: 1
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- 什么是移动应用开发-关于移动应用开发的相关介绍
- 第二组汇报 PPT.pptx
- 什么是大数据开发-相关介绍-关于大数据开发的相关介绍
- 什么是软件测试-相关介绍-关于软件测试的相关介绍
- 前端开发-什么是前端开发-关于前端开发的一些相关介绍
- Sora AI-关于文生视频的使用场景说明
- suno AI文生视频的相关教程和介绍使用
- 什么是后端开发-关于后端开发的一些小介绍分享
- Jurassic Pack Vol. II Dinosaurs 侏罗纪包卷恐龙二号Unity游戏模型资源unitypackage
- Jurassic Pack Vol. III Dinosaurs 侏罗纪包卷恐龙三号Unity游戏模型资源unitypackag
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功